Single-Sign-On By Vouch Proxy And AWS Cognito
Abstract
- For Kubernetes cluster, we have many observability and monitoring tools which are built-in with separated dashboard/console UIs with login-authentication. We don't want to create many domains as well as multiple accounts to handle them. This post introduces vouch proxy as a solution to provide single-sign on which supports many OAuth and OIDC login providers and can enforce authentication to AWS Cognito user pool.
Table Of Contents
🚀 Vouch Proxy Overview
Vouch Proxy - An SSO solution for Nginx using the auth_request module. Vouch Proxy can protect all of your websites at once.
Vouch Proxy supports many OAuth and OIDC login providers and can enforce authentication to... This blog introduces applying vouch-proxy with AWS Cognito userpool
In this blog post, we apply this solution for Applications such as Solr Cloud, AKHQ, and glowroot in Kubernetes cluster where vouch proxy and nginx are also deployed on.
🚀 What Exactly Vouch Proxy Does
Diagram
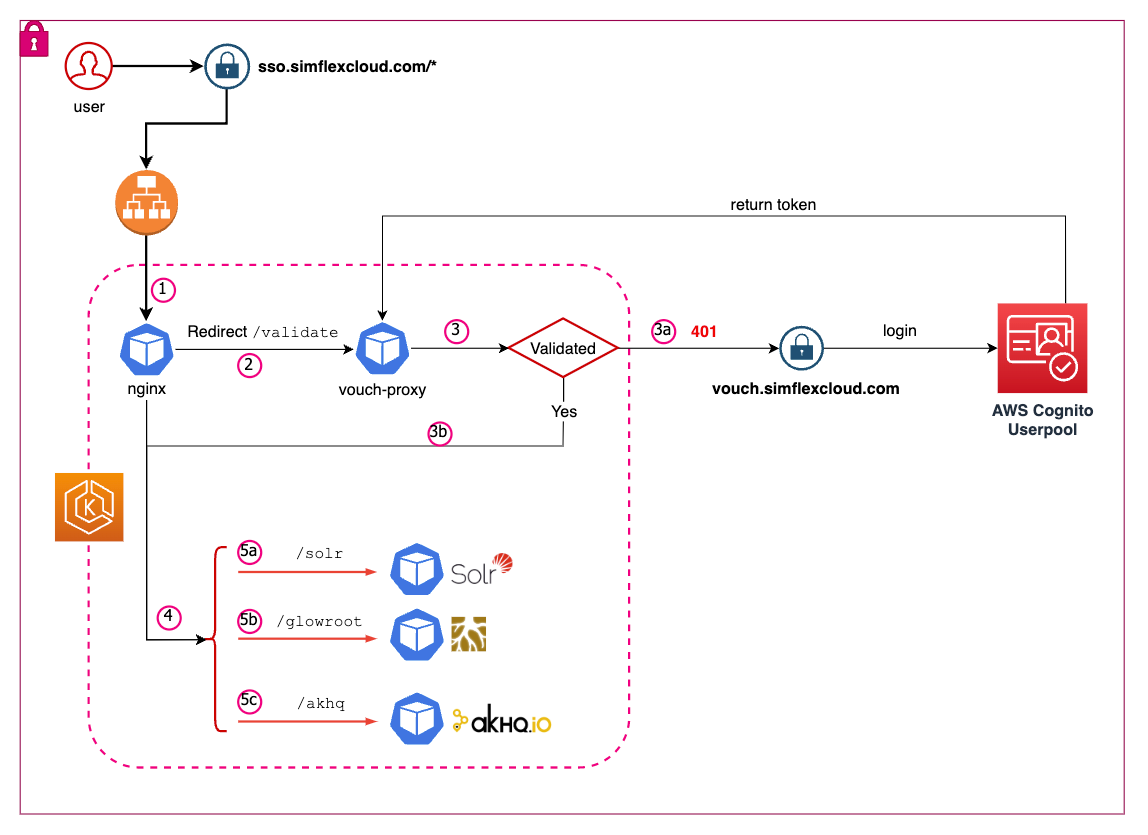
The flows
User access to one of the subpaths such as
/solrfor Solr Admin UI through https://sso.simflexcloud.com/solrThe request is go to AWS Application load balancer and then forwarded to NGINX target group
Nginx authorizes the request by calling/validating the request using vouch-proxy through the internal endpoint
http://vouch:9090/validateof kubernetes serviceVouch-proxy validates and returns 200 if the user already has the cache login token or returns
401if not yet performed loginWith 200 code, the request is redirected to the target location here is Solr UI admin
With 401 code, the request is redirected to
https://vouch.simflexcloud.com/login?url=https://$http_host$request_uri&vouch-failcount=$auth_resp_failcount&X-Vouch-Token=$auth_resp_jwt&error=$auth_resp_err>to login, if the login is successful, the request is redirected to the target location here is Solr UI admin
Default redirect is the main page or marketing page or anything you would like to show as your SSO
🚀 How does vouch-proxy protect the domains?
Vouch-proxy (VP) supports many OAuth and OIDC login providers to authentication
Furthermore, vouch-proxy whitelists the domains, not only the access domain but also the domain of email login. The cookie domain, the domain that VP is served from and the protected app must all be the same domain. For example, if we just whitelist the app domain such as simflexcloud.com but the email is
simflex.cloud@gmail.comit will not authorize the user2022-07-07T15:58:12.716Z WARN /auth User is not authorized: verifyUser: Email simflex.cloud@gmail.com is not within a Vouch Proxy managed domain . Please try again or seek support from your administrator
🚀 Setup AWS Cognito as authorised provider
Pre-requisite: You already create login to user for login authentication.
Cognito userpool application client

Setup vouch-proxy config with AWS Cognito, replace the URLs with one's setup from Cognito
vouch: logLevel: debug port: 9090 cookie: secure: false domains: # app domain and mail domain only - simflexcloud.com - gmail.com oauth: provider: oidc client_id: AWS_COGNITO_VOUCH_CLIENT_ID auth_url: <https://{yourCognitoDomain}.amazoncognito.com/oauth2/authorize> token_url: <https://{yourCognitoDomain}.amazoncognito.com/oauth2/token> user_info_url: <https://{yourCognitoDomain}.amazoncognito.com/oauth2/userInfo> scopes: - openid - email - profile callback_url: <https://{callbackURL}/auth>
🚀 Deploy vouch-proxy and nginx
Go to nginx to get Dockerfile, nginx config files to build the
nginx-gwimageUse the
quay.io/vouch/vouch-proxyimage to start vouch-proxy by mounting the config file to/config/config.yml
🚀 Troubleshooting
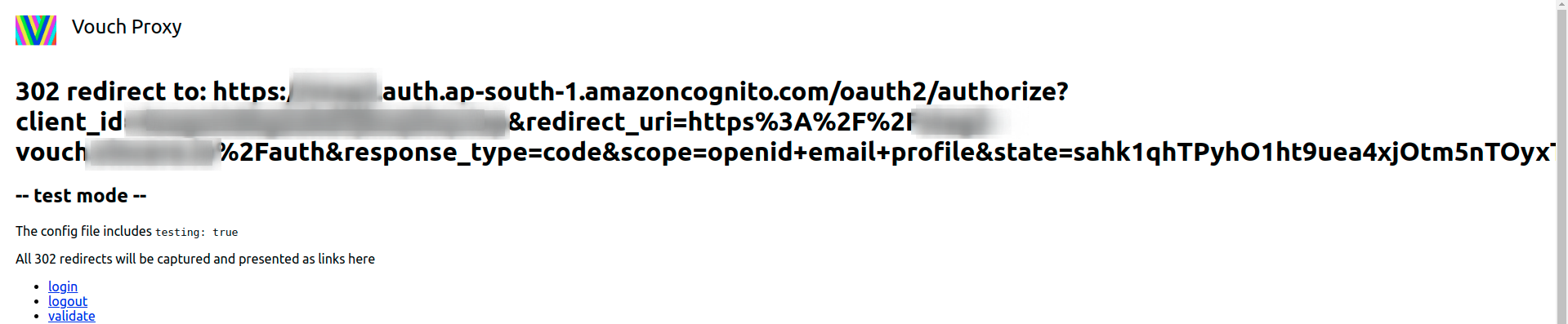
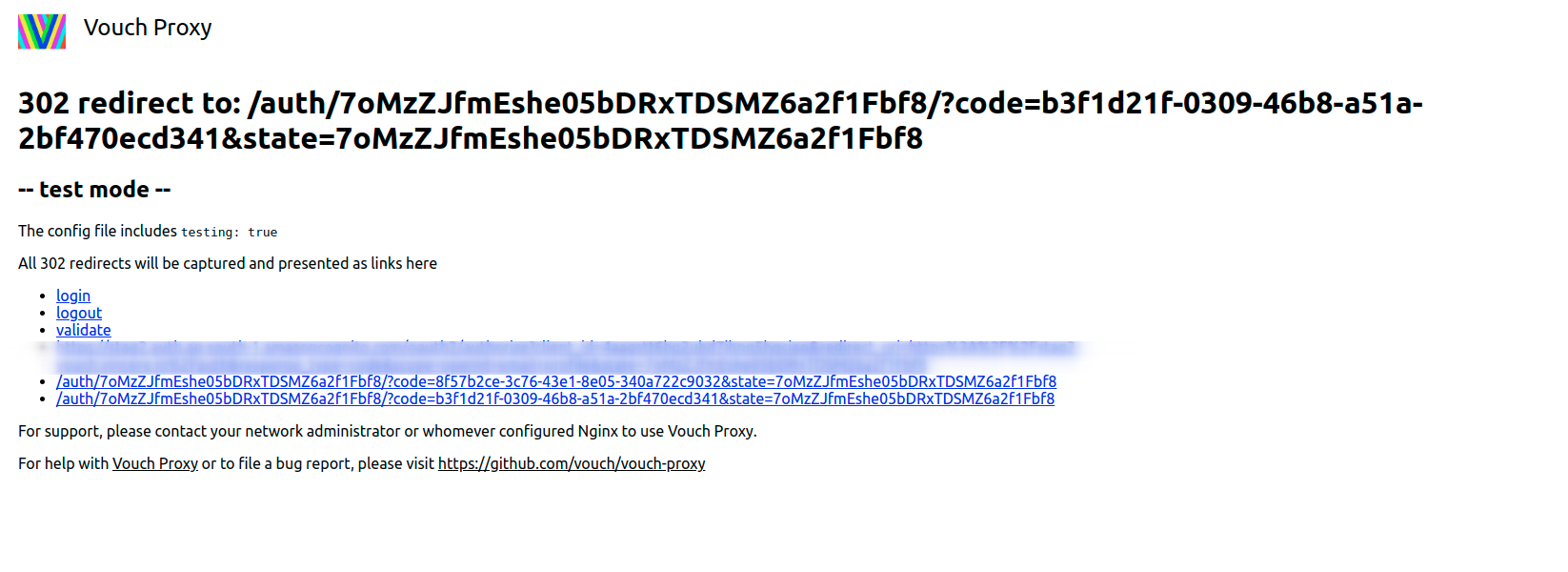
Getting started to align between Nginx, Vouch Proxy and your identity provider (IdP) can be tricky, vouch-proxy provides a config to enable the testing mode
vouch: testing: true logLevel: debugWith testing enable, the UI will step us to each phase of redirecting
🚀 Conclusion
- Now we have SSO domain to access all the services conveniently and it's possible to add any more subpath for other services. The session with Cognito userpool token has expired time and we can update this timeout through Cognito attributes.